Cybersecurity Solutions for Small Businesses in Orlando, Florida
Orlando businesses operate in a highly connected environment, relying on cloud platforms, remote access, third-party vendors, and digital customer interactions. While this connectivity improves efficiency, it also expands the attack surface that cybercriminals actively target. Protect your operations, data, and reputation with enterprise-grade cybersecurity built specifically for Orlando SMB's.
Cybersecurity Built for Orlando Small Businesses
Unlike large enterprises with internal security teams, most SMBs must balance cybersecurity against limited resources and competing priorities. According to guidance from the U.S. Small Business Administration, small businesses are frequently targeted precisely because attackers expect weaker defenses.
Orlando’s concentration of professional services, healthcare providers, and hospitality businesses creates a high-value environment for attackers seeking sensitive data and credential access. The National Institute of Standards and Technology (NIST) emphasizes that organization size does not reduce risk—attackers exploit opportunity, not scale.
Kelley Information Technology delivers cybersecurity solutions designed specifically for Orlando small businesses. Our approach focuses on real-world risk, local industry conditions, and practical protection that supports business continuity rather than slowing it down.

Cybersecurity Solutions Your Business Relies On
Talk to a Cybersecurity Specialist
Get expert guidance tailored to your Orlando business.
Protect Your Orlando Business from Cyber Threats
Cybersecurity is a business decision that directly impacts trust, uptime, and long-term stability. Connect with Kelley Information Technology to discuss how we can support your cybersecurity goals.
What Cybersecurity Solutions Mean for Small Businesses
Cybersecurity solutions encompass the policies, technologies, processes, and controls used to protect business systems, data, and users from digital threats. For small businesses in Orlando, cybersecurity is not limited to antivirus software or firewalls—it includes identity protection, endpoint security, network controls, cloud security, monitoring, and incident response. The National Institute of Standards and Technology defines cybersecurity as an ongoing risk management discipline rather than a static technical implementation. This distinction is critical for Orlando SMBs, where technology environments evolve rapidly due to cloud adoption, remote work, and third-party integrations.
At its core, cybersecurity exists to preserve three fundamental business objectives: confidentiality, integrity, and availability. Confidentiality ensures that sensitive information such as customer records, financial data, and proprietary business information remains protected from unauthorized access. Integrity ensures systems and data are not altered maliciously or accidentally, while availability ensures your business can continue operating even when threats or failures occur.
For Orlando SMB's supporting cloud platforms, remote employees, and third-party access, Cybersecurity significantly reduces the risk of credential abuse, ransomware propagation, and unauthorized data access. Kelley Information Technology delivers cybersecurity as a managed, continuously improving service. Rather than installing disconnected tools, we build coordinated security programs that adapt as your business grows, regulations change, and threats evolve.
Secure Your Business NowWhy Cybersecurity Matters for Orlando Small Businesses
Orlando is home to a diverse small business ecosystem that includes professional services firms, healthcare providers, hospitality organizations, creative agencies, and education-focused institutions. These businesses rely heavily on digital systems to operate efficiently, store sensitive information, and serve customers. As a result, cybersecurity failures have immediate and far-reaching consequences.
Cyber incidents frequently result in extended downtime for small businesses because recovery resources are limited. According to the U.S. Small Business Administration, many small businesses struggle to recover financially after a major cyber event, particularly when operations are disrupted for days or weeks.
Beyond operational impact, Orlando businesses face increasing pressure from clients, partners, and insurers to demonstrate responsible cybersecurity practices. Cyber insurance providers are raising security requirements, contracts increasingly include data protection clauses, and regulatory scrutiny continues to expand across healthcare, legal, and education sectors.
The Cybersecurity and Infrastructure Security Agency emphasizes that proactive cybersecurity reduces both the likelihood and severity of incidents. For Orlando SMBs, this means fewer disruptions, lower financial exposure, and stronger trust with customers and stakeholders.
Protect Your Network Today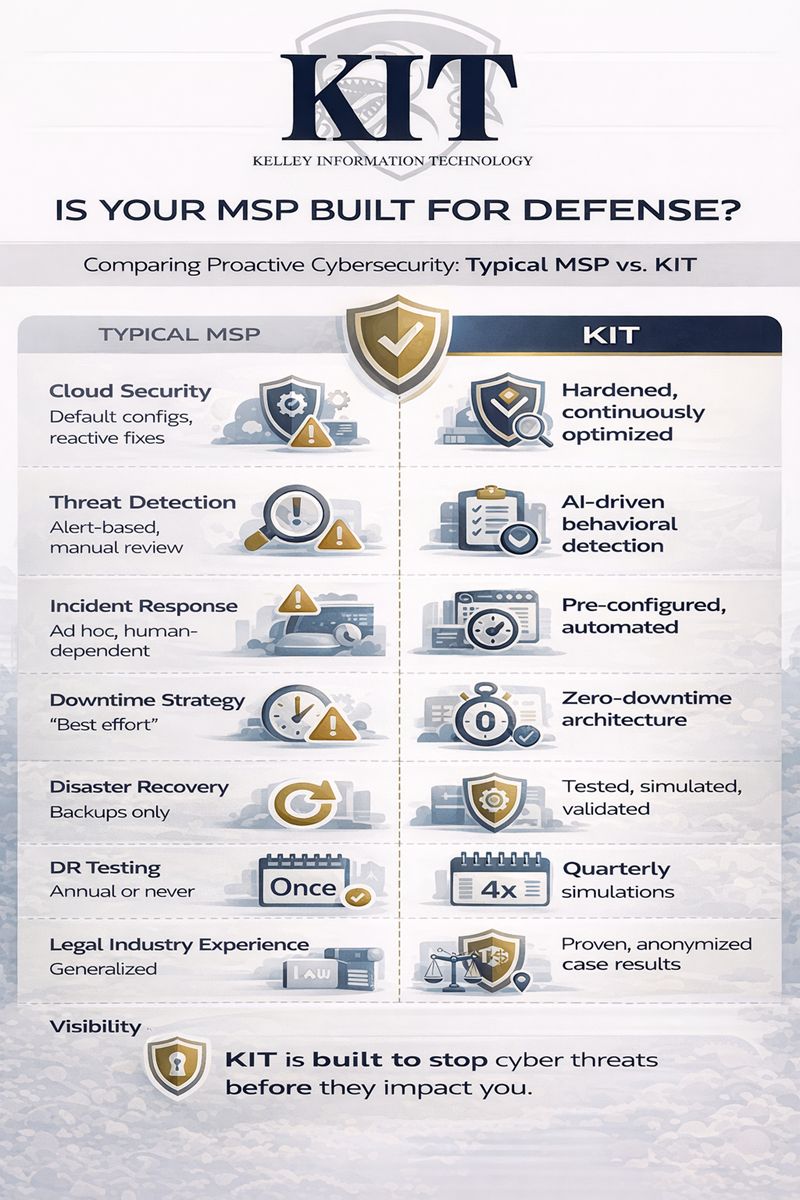
Cybersecurity Solutions Built for Orlando SMBs
Effective cybersecurity is not a single product—it is a coordinated system of controls designed to prevent, detect, and respond to threats without disrupting business operations. Orlando small businesses depend on secure access to systems, cloud platforms, and client data to remain competitive.
Improve Your Cyber DefenseCybersecurity Is a Core Business Requirement for Orlando Small Businesses
Cybersecurity is no longer a concern reserved for large enterprises — it is a fundamental requirement for small businesses operating in Orlando’s growing professional and service-based economy. According to the Verizon Data Breach Investigations Report (DBIR), nearly half of all reported cyber incidents impact small and midsize organizations. Modern attacks are highly automated, meaning threat actors do not manually select targets — they exploit exposed systems wherever they find them. For local businesses that rely on cloud platforms, remote access, and customer data, this reality makes proactive cybersecurity essential for operational continuity.
Upgrade Your Security StrategyThe Financial Impact of Cyber Incidents Is Disproportionately Severe for Small Firms
While global breach statistics often highlight enterprise-level losses, the underlying data reveals why smaller organizations face outsized consequences. The IBM Cost of a Data Breach Report consistently shows that incident response delays, lack of preparedness, and downtime significantly increase recovery costs. For small businesses, even short service interruptions can disrupt cash flow, damage customer trust, and create long-term reputational harm. Without structured security planning, recovery timelines stretch longer and costs escalate faster.
Reduce Cyber Risk FastMost Attacks Exploit Preventable Gaps in Access and User Security
Industry data shows that the majority of successful breaches stem from compromised credentials, phishing, and misconfigured systems rather than advanced zero-day exploits. The Cybersecurity and Infrastructure Security Agency (CISA) identifies phishing and weak authentication controls as leading causes of ransomware and data-theft incidents. These threats thrive in environments without multi-factor authentication, employee awareness training, and consistent patch management — gaps that are common in small business IT environments without a defined security framework.
Harden Your Security PerimeterThe KIT Methodology Applies Layered, Standards-Based Protection
KIT’s cybersecurity methodology is built around proven best practices aligned with frameworks such as the NIST Cybersecurity Framework. We focus on layered defense — combining identity security, endpoint protection, network monitoring, secure backups, and continuous risk assessment. By addressing both technical controls and human behavior, KIT helps Orlando small businesses reduce attack surfaces, detect threats earlier, and respond decisively when incidents occur.
Enhance Your Threat ProtectionProactive Cybersecurity Strengthens Trust and Long-Term Business Resilience
Effective cybersecurity is not just about avoiding breaches — it’s about enabling confident growth. Organizations that implement structured security practices are better positioned to meet regulatory expectations, protect customer data, and maintain operational stability. Guidance from the Federal Trade Commission (FTC) emphasizes that reasonable security safeguards are now an expectation, not a differentiator. By embedding cybersecurity into daily operations through the KIT approach, Orlando businesses build resilience, credibility, and long-term competitive strength.
See How KIT Secures Your BusinessProtect Your Orlando Business from Cyber Threats
Cybersecurity is a business decision that directly impacts trust, uptime, and long-term stability. Connect with Kelley Information Technology to discuss how we can support your cybersecurity goals.
Defense-in-Depth: Why Layered Security Work
Defense-in-depth is a cybersecurity strategy based on the principle that no single control can stop every threat. Instead, multiple layers of protection work together to detect, prevent, and contain attacks. The National Institute of Standards and Technology consistently reinforces this model as the most effective way to manage cyber risk across organizations of all sizes.
Layered security also supports business continuity. By containing incidents quickly, organizations can maintain operations, protect customer trust, and avoid the prolonged downtime that often follows major cyber events. This transforms cybersecurity from a reactive expense into a proactive business safeguard. For Orlando small businesses, defense-in-depth means combining endpoint protection, network security, identity controls, cloud safeguards, monitoring, and response capabilities into a cohesive system. If one layer fails, another is positioned to limit impact and prevent escalation.
Protect Your Team With KIT Security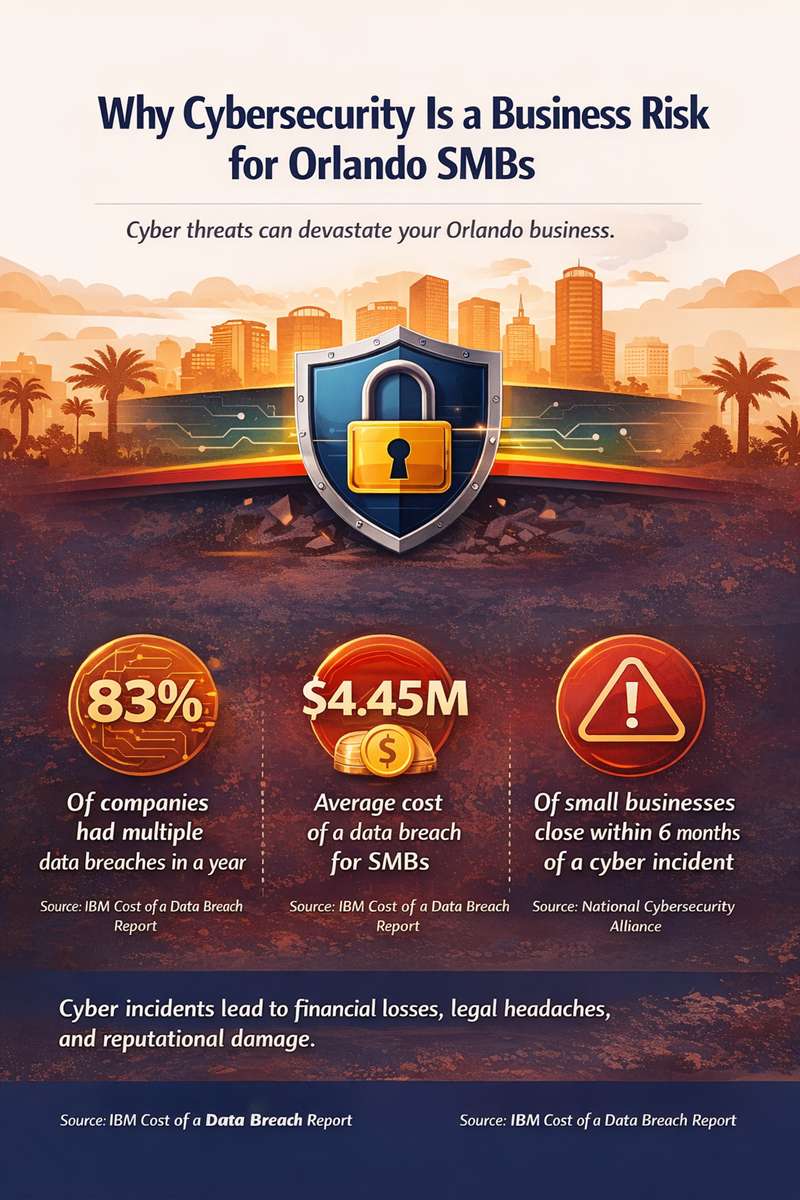

Core Components of Cybersecurity Security
A successful Cybersecurity implementation integrates identity management, endpoint security, network segmentation, and continuous monitoring into a unified security framework.
Kelley Information Technology designs Cybersecurity architectures that align with your existing IT environment while minimizing disruption to daily operations.
Build a Stronger Security FrameworkThe Real Cybersecurity Risk Facing Small Businesses
Cybersecurity threats disproportionately impact small businesses, not because they are less important, but because attackers know they are often less protected. Data from the FBI’s Internet Crime Complaint Center consistently shows that phishing, ransomware, and business email compromise remain among the most financially damaging cybercrime categories affecting U.S. businesses.

Core Cybersecurity Services We Provide
Effective cybersecurity requires multiple layers of protection working together. A single control cannot stop every threat, which is why our cybersecurity solutions are designed as an integrated system rather than a collection of standalone tools.
Start Your KIT Cybersecurity PlanManaged Security Monitoring and Response
Continuous monitoring is essential for identifying suspicious activity before it escalates into a full-scale incident. Our managed security monitoring aligns with guidance from the Cybersecurity and Infrastructure Security Agency, which stresses early detection as one of the most effective ways to reduce breach impact for small organizations.
Partner With KIT for Cyber DefenseEndpoint Protection and Device Security
Every device connected to your environment represents a potential entry point for attackers. Modern endpoint protection extends beyond traditional antivirus by incorporating behavior-based detection, exploit prevention, and automated containment. The National Institute of Standards and Technology identifies endpoint security as a foundational control for reducing attack surface in SMB environments.
Explore Cybersecurity SolutionsNetwork Security and Segmentation
Once attackers gain access, they often move laterally across networks to reach critical systems. We design secure network architectures using segmentation, firewall enforcement, and access controls to limit exposure. The U.S. Small Business Administration highlights network misconfiguration as a frequent contributor to successful small business attacks.
Business Cyber Protection ToolsCloud and Email Security
Cloud platforms and email systems are among the most targeted assets for small businesses. Data published by the FBI’s Internet Crime Complaint Center shows that business email compromise continues to generate billions in annual losses. Our cybersecurity solutions include advanced email filtering, identity protection, and cloud access controls to reduce these risks.
Advanced Threat PreventionCompliance-Oriented Security Controls
For businesses operating in regulated industries, cybersecurity must support compliance without disrupting operations. We design controls that align with regulatory expectations while remaining practical for Orlando small businesses with limited internal resources.
Zero Trust Security for TeamsDon’t Wait Until a Cyber Incident Disrupts Your Business
Proactive threat detection and a tested incident response plan can mean the difference between a minor security event and weeks of downtime.
Get My Incident Readiness AssessmentCybersecurity Solutions for Key Orlando Industries
While every small business faces cybersecurity risk, the nature of that risk varies significantly by industry. Regulatory obligations, data sensitivity, operational workflows, and threat exposure differ across sectors. Kelley Information Technology tailors cybersecurity solutions to align with these industry-specific realities while maintaining a consistent, risk-based foundation.
Cybersecurity for Modern WorkCybersecurity for Legal Practices
Law firms manage confidential client communications, privileged documents, and sensitive case materials that demand strict protection. Guidance from the American Bar Association underscores the ethical obligation attorneys have to safeguard client data in digital environments.
Our work supporting law firms with specialized IT and cybersecurity requirements focuses on access controls, encryption, secure document handling, and audit trails that protect confidentiality without disrupting legal workflows.
Secure My BusinessCybersecurity for Creative Agencies
Creative agencies rely on collaboration, cloud-based file sharing, and distributed teams to deliver work efficiently. Intellectual property theft and unauthorized access to client assets represent significant risks. The National Institute of Standards and Technology identifies intellectual property protection as a growing concern in digitally collaborative environments.
We design security strategies tailored to creative agency workflows that protect cloud platforms and endpoints while preserving the speed and flexibility creative teams depend on.
Protect My DataCybersecurity for Hospitality Businesses
Hospitality organizations manage guest data, payment card information, reservation systems, and public-facing networks. These environments face constant exposure due to high transaction volume and third-party integrations. Standards published by the Payment Card Industry Security Standards Council emphasize segmentation and access control as essential safeguards.
Our experience delivering hospitality-focused IT and cybersecurity solutions prioritizes network segmentation, monitoring, and rapid containment to protect guest trust and business continuity.
Stop Cyber ThreatsCybersecurity for Healthcare Providers
Healthcare organizations handle protected health information and operate under strict regulatory oversight. The U.S. Department of Health and Human Services consistently reports healthcare as one of the most targeted sectors for cyberattacks due to the value of patient data.
We implement cybersecurity controls that support compliance, protect patient information, and ensure system availability for Orlando healthcare providers without interfering with care delivery.
Strengthen SecurityCybersecurity for Education Organizations
Educational institutions manage student records, staff data, and digital learning platforms, often with limited IT resources. The Cybersecurity and Infrastructure Security Agency has identified education as a sector experiencing increased ransomware and credential theft activity.
Our cybersecurity solutions for education-focused organizations emphasize identity protection, endpoint security, and monitoring that aligns with budget and operational constraints.
Start Security ReviewBusiness Outcomes With Cybersecurity in Action
Implementing Cybersecurity is not just a technical upgrade—it delivers measurable business outcomes for Orlando organizations focused on growth, compliance, and operational resilience.
Businesses adopting Cybersecurity best-practices experience reduced breach impact, improved regulatory alignment, stronger cloud security posture, and increased confidence supporting remote and hybrid employees without sacrificing protection.
By enforcing identity-based access controls and continuous verification, Cybersecurity enables secure scalability while maintaining predictable IT risk management.
Explore Cybersecurity SolutionsReal-World KIT Implemented Cybersecurity Solutions
Kelley Information Technology has implemented cybersecurity and IT solutions for organizations across Central Florida. These engagements demonstrate how security must adapt to industry-specific workflows while maintaining consistent protection standards.
- LAW FIRMS
CREATIVE AGENCIES
HOSPITALITY
Why Orlando Businesses Choose Kelley Information Technology
Kelley Information Technology specializes in cybersecurity solutions designed specifically for small and mid-sized businesses in Central Florida. We understand the operational realities, budget constraints, and risk profiles SMBs face every day. Our threat detection and incident response services are built on proven frameworks, real-world experience, and guidance from organizations like NIST and CISA. We don’t just respond to incidents—we help Orlando businesses prepare, reduce risk proactively, and recover with confidence.
Strengthen Your Cybersecurity Posture